What is Korifi?
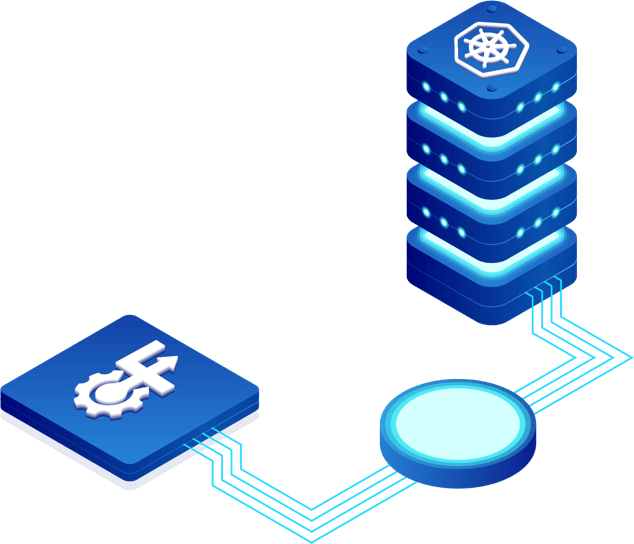
Korifi is an open-source platform that simplifies the deployment and management of cloud-native applications on Kubernetes. Built by the Cloud Foundry community, Korifi delivers an inherently higher-order abstraction of Kubernetes, enabling developers to focus on building applications. With Korifi, development teams of all sizes can leverage the power of Kubernetes with fewer complexities, enabling them to deploy applications faster and more efficiently.
Open-Source Platform
One-Command Deployments
Full-Scale Operations
Dev Complete. Ops Ready
Korifi seamlessly integrates into your DevOps toolchain for container orchestration, providing support across the full application lifecycle. It includes Kubernetes-native tools such as Envoy and kpack, while allowing development teams to extend their existing CI/CD, logging, and observability services. With Korifi, even small teams and startups can adopt best practices for developing, testing, deploying, and managing containerized applications on Kubernetes.
Learn Korifi From Tutorials
Discover all of Korifi's capabilities by exploring our collection of community-built tutorials, designed to cater to all experience levels. Whether you're a beginner eager to get up and running quickly or an experienced Korifi user looking to hone your skills, there's a tutorial for you.
Designed for Multi-Cloud, Multi-Tenant, and Polyglot Needs

Using a combination of different public cloud infrastructures for diverse staging needs? Have strict compliance requirements around on-premise servers? Running Kubernetes clusters on the edge? No problem! Korifi can help deploy cloud-native apps to any permutation of infrastructure types, including on-premises, multiple clouds, and public cloud infrastructures. This allows app developers to deploy cloud-native apps on any remote environment with ease.
Korifi utilizes Kubernetes RBAC and CRDs to mimic the robust Cloud Foundry paradigm of orgs and spaces. Together, the two provide a foundation for multi-tenancy that is resilient and secure.
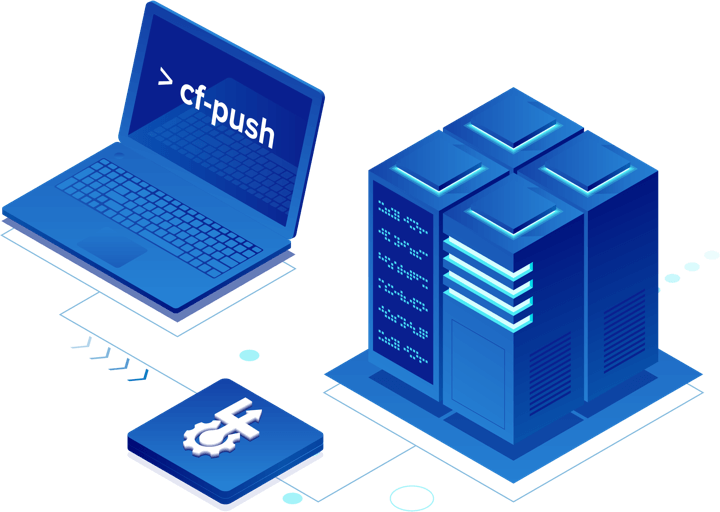
Korifi preserves the classic Cloud Foundry experience of being able to deploy apps written in any language or framework with a single cf-push command. It further enhances the app developer experience by using Paketo buildpacks to deploy apps as OCI-compatible containers. App developers no longer have to wrangle with complex YAML or Dockerfiles for containerized applications run on Kubernetes.