How to Make Your Developer Experience Immune to the COVID-19 Crisis
by Caitlyn O'Connell July 7, 2020
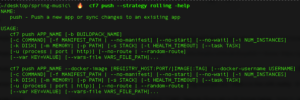
Cloud Foundry Further Simplifies Modern App Development: An Inside Look at the New cf CLI v7
by Josh Collins June 24, 2020

How to Use App Revisions with Cloud Foundry V3 API
by Seth Boyles August 6, 2019
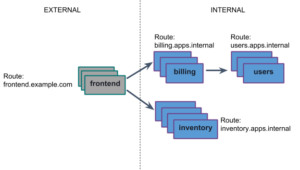
Polyglot Service Discovery for Container Networking in Cloud Foundry
by Usha Ramachandran March 9, 2018
Scroll Left
Scroll Right
community
See All
Scroll Left
Scroll Right
ecosystem
See All
Scroll Left
Scroll Right
engineering
See All
Scroll Left
Scroll Right
app dev
See All
Scroll Left
Scroll Right
foundation
See All
Scroll Left
Scroll Right
press release
See All
Scroll Left
Scroll Right
user stories
See All
Orange Makes Novel Use of Cloud Foundry for Best Developer Experience
by Caitlyn O'Connell 7.15.2019
Scroll Left
Scroll Right
videos
See All
Scroll Left
Scroll Right
security advisory
See All
Scroll Left
Scroll Right